Cybersecurity in 2026: Federal Compliance & Cost Implications for US Businesses

The digital frontier is constantly expanding, and with it, the threats that loom within. For US businesses, the year 2026 is poised to be a landmark year, bringing with it a wave of new federal cybersecurity compliance standards. These aren’t just minor adjustments; they represent a significant shift in how organizations are expected to protect sensitive data and critical infrastructure. The implications are far-reaching, touching every aspect of business operations, from IT infrastructure to employee training, and perhaps most critically, the financial bottom line. Understanding these forthcoming changes, their potential costs, and how to prepare is not merely advisable but absolutely essential for survival and prosperity in the evolving digital landscape.
The urgency behind these new regulations stems from a confluence of factors: the escalating sophistication of cyberattacks, the increasing frequency of data breaches, and the growing recognition that national security and economic stability are inextricably linked to robust cybersecurity. Federal agencies, having observed the vulnerabilities exposed in recent years, are now moving to codify and enforce a higher standard of digital hygiene across various sectors. This proactive stance aims to create a more resilient national cybersecurity posture, protecting both government interests and private sector assets.
For many businesses, particularly small and medium-sized enterprises (SMEs) that often operate with limited resources, navigating this complex regulatory environment can feel daunting. The sheer volume of information, the technical jargon, and the potential for hefty fines for non-compliance can be overwhelming. However, viewing these new standards as an unavoidable burden would be a mistake. Instead, they should be seen as an opportunity – an impetus to strengthen defenses, build trust with customers, and ultimately, secure a competitive advantage in a world where digital trust is paramount.
This comprehensive guide will delve deep into the anticipated Federal Cybersecurity Compliance 2026 standards. We will explore the key regulatory bodies driving these changes, the specific requirements likely to be imposed, and the tangible cost implications for US businesses. Furthermore, we will provide actionable strategies and best practices to help your organization not only meet but exceed these new benchmarks, transforming compliance from a challenge into a strategic asset.
The Evolving Landscape of Federal Cybersecurity Regulations
Before we dissect the specifics of 2026, it’s crucial to understand the trajectory of federal cybersecurity regulations. Over the past decade, we’ve witnessed a gradual but steady increase in the emphasis on cybersecurity, driven by a series of high-profile incidents and a growing awareness of systemic vulnerabilities. Frameworks like the National Institute of Standards and Technology (NIST) Cybersecurity Framework have become de facto standards, guiding organizations in establishing and improving their cyber risk management programs. Similarly, sector-specific regulations, such as HIPAA for healthcare and PCI DSS for payment card industry, have long mandated specific security controls.
What makes 2026 different is the anticipated consolidation and expansion of these efforts, potentially leading to more harmonized yet more stringent requirements across a broader spectrum of industries. The Biden administration has signaled a strong commitment to bolstering national cybersecurity, issuing executive orders that emphasize information sharing, supply chain security, and the adoption of zero-trust architectures. These high-level directives are now being translated into concrete regulations that will impact how businesses operate.
Key Drivers for New 2026 Standards
- Increased Sophistication of Threats: Ransomware, supply chain attacks, and state-sponsored cyber espionage have reached unprecedented levels of complexity and impact.
- Critical Infrastructure Protection: A heightened focus on securing essential services like energy, water, transportation, and healthcare from cyber disruption.
- Data Privacy Concerns: The ongoing debate around data privacy, both at federal and state levels, is influencing how data is collected, stored, and protected.
- Supply Chain Vulnerabilities: The realization that a single weak link in a supply chain can compromise an entire ecosystem has led to a push for greater oversight of third-party vendors.
- International Harmonization: Efforts to align US standards with international best practices to facilitate global commerce and information sharing while maintaining security.
These drivers collectively underscore the necessity for a robust and adaptive regulatory framework. The 2026 standards are expected to reflect this urgency, moving beyond mere recommendations to enforceable mandates with clear penalties for non-compliance. Therefore, US businesses must begin their preparation now to avoid being caught off guard.
Anticipated Federal Cybersecurity Compliance Standards for 2026
While the exact legislative texts are still being finalized, patterns and pronouncements from federal agencies offer clear indications of what to expect for Federal Cybersecurity Compliance 2026. The overarching theme is a move towards more prescriptive, auditable, and risk-based approaches to cybersecurity.
NIST Framework Integration and Expansion
The NIST Cybersecurity Framework (CSF) is likely to remain a cornerstone, but expect its application to become more mandatory and granular. Businesses might be required to demonstrate not just alignment with the framework, but specific implementation of its five core functions: Identify, Protect, Detect, Respond, and Recover. This could involve:
- Mandatory Risk Assessments: Regular, comprehensive risk assessments that identify assets, threats, vulnerabilities, and the potential impact of cyber incidents.
- Enhanced Access Controls: Stricter requirements for multi-factor authentication (MFA), least privilege access, and regular review of user permissions.
- Robust Incident Response Plans: Detailed, tested incident response plans that cover detection, containment, eradication, recovery, and post-incident analysis.
- Continuous Monitoring: Real-time monitoring of network activity, system logs, and security events to detect and respond to threats promptly.
- Data Encryption: Mandated encryption for data at rest and in transit, especially for sensitive personal identifiable information (PII) and protected health information (PHI).
CMMC 2.0 and Supply Chain Security
For businesses contracting with the Department of Defense (DoD), the Cybersecurity Maturity Model Certification (CMMC) 2.0 will be fully operational and highly enforced. CMMC 2.0 simplifies the previous version into three levels (Foundational, Advanced, Expert) but tightens the audit requirements. This framework is a bellwether for broader supply chain security initiatives across the federal government. Companies not directly contracting with the DoD but serving as suppliers to federal contractors may also find themselves indirectly subject to CMMC-like requirements, as prime contractors flow down these mandates.
The emphasis here is on verifiable security practices, moving beyond self-attestation to requiring third-party assessments for higher maturity levels. This will undoubtedly influence other sectors as the federal government seeks to fortify its entire digital ecosystem.
Sector-Specific Regulations and Harmonization
While general federal standards will apply broadly, specific industries will likely see updates to their existing regulatory frameworks. For instance:
- Financial Services: Updates to GLBA (Gramm-Leach-Bliley Act) and potential new mandates from the SEC (Securities and Exchange Commission) regarding cyber risk disclosure and governance.
- Healthcare: Stricter enforcement of HIPAA, with increased scrutiny on cloud providers and business associates handling PHI.
- Energy & Utilities: NERC CIP (North American Electric Reliability Corporation Critical Infrastructure Protection) standards will continue to evolve, with a focus on operational technology (OT) security.
- Critical Infrastructure (Broader Scope): Expect the Cybersecurity and Infrastructure Security Agency (CISA) to play a more prominent role, potentially issuing binding directives for designated critical infrastructure entities, even those not traditionally thought of as federal contractors.
A key trend will be the push for greater harmonization. While sector-specific rules will persist, federal agencies are likely to try and reduce redundant requirements where possible, aiming for a more streamlined, albeit rigorous, compliance landscape.

Cost Implications for US Businesses
Meeting the new Federal Cybersecurity Compliance 2026 standards will undoubtedly incur significant costs for US businesses. These costs are multifaceted, extending beyond mere software purchases to encompass personnel, training, and ongoing operational expenses. It’s crucial for businesses to budget appropriately and plan proactively to mitigate financial shocks.
Direct Costs of Compliance
- Technology Investments:
- Security Software and Hardware: Upgrading firewalls, intrusion detection/prevention systems (IDS/IPS), endpoint detection and response (EDR) solutions, security information and event management (SIEM) systems, data loss prevention (DLP) tools, and encryption technologies.
- Cloud Security: Investments in cloud access security brokers (CASB), secure configuration management for cloud environments, and cloud-native security tools.
- Identity and Access Management (IAM): Implementing robust IAM solutions, including multi-factor authentication (MFA), single sign-on (SSO), and privileged access management (PAM).
- Personnel and Expertise:
- Hiring Security Professionals: The demand for skilled cybersecurity professionals (CISOs, security analysts, incident responders) will surge, leading to higher salaries and recruitment costs.
- Training and Upskilling: Investing in training for existing IT staff on new security technologies and compliance requirements.
- Consultants and Auditors: Engaging third-party cybersecurity consultants for gap analyses, risk assessments, penetration testing, and pre-audits. For CMMC, certified third-party assessment organizations (C3PAOs) will be mandatory for certain levels.
- Process and Policy Development:
- Documentation: Developing, updating, and maintaining comprehensive security policies, procedures, and incident response plans.
- Compliance Management Solutions: Software to help track compliance status, manage evidence, and automate reporting.
- Third-Party Vendor Management:
- Due Diligence: Increased costs associated with evaluating the cybersecurity posture of all third-party vendors and supply chain partners.
- Contractual Obligations: Renegotiating contracts to include stringent cybersecurity clauses and audit rights.
Indirect Costs and Risks of Non-Compliance
Beyond the direct expenditures, businesses face significant indirect costs and risks if they fail to meet the 2026 standards:
- Fines and Penalties: Federal regulations often carry substantial financial penalties for non-compliance, which can quickly outweigh the cost of proactive investment.
- Reputational Damage: Data breaches or public non-compliance can severely damage a company’s reputation, leading to loss of customer trust and market share.
- Legal Fees and Litigation: Non-compliance can expose businesses to lawsuits from affected parties, significantly increasing legal expenses.
- Loss of Federal Contracts: For federal contractors, failure to comply with CMMC or other requirements will result in immediate disqualification from lucrative government contracts.
- Business Disruption: Cyber incidents, often a consequence of poor security posture, can lead to operational downtime, lost revenue, and recovery costs.
- Increased Insurance Premiums: Cybersecurity insurance premiums are already rising, and non-compliance will likely lead to even higher costs or denial of coverage.
It’s clear that the costs of non-compliance far outweigh the initial investment required to achieve and maintain adherence to the new standards. Proactive investment is not just about meeting a mandate; it’s about safeguarding the future viability of the business.
Strategies for Achieving Federal Cybersecurity Compliance 2026
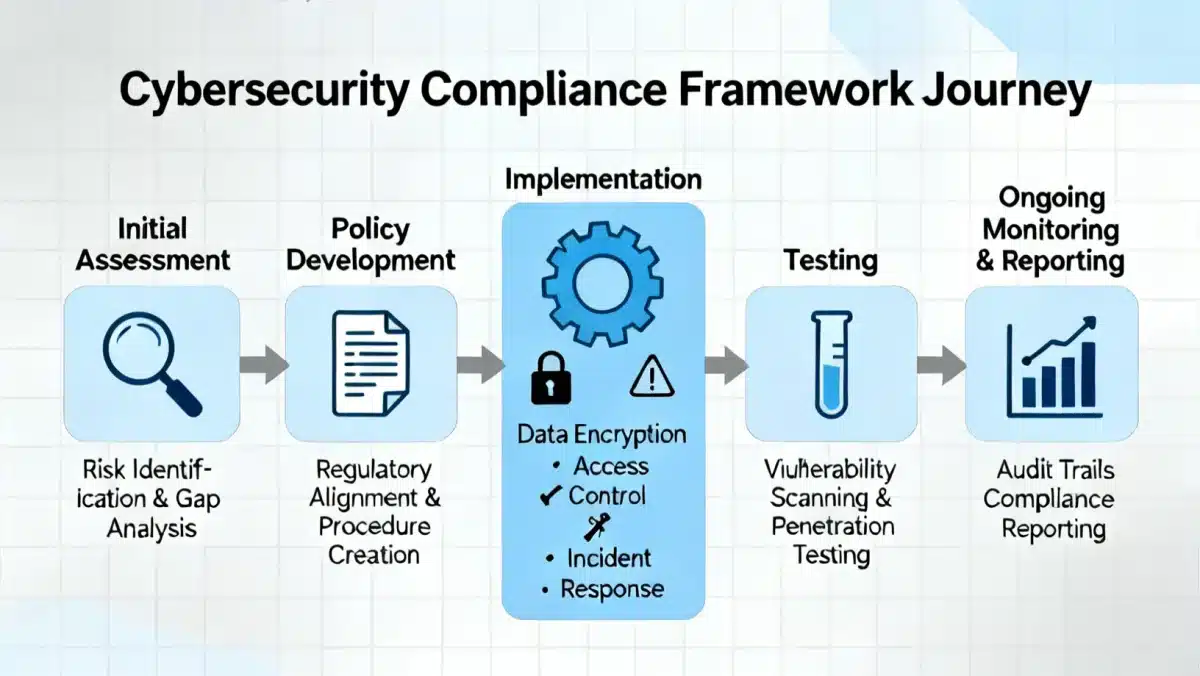
Preparing for the 2026 federal cybersecurity compliance standards requires a strategic, multi-faceted approach. Businesses should view this as an ongoing journey rather than a one-time project. Here are key strategies:
1. Conduct a Comprehensive Gap Analysis
The first step is to understand where your organization currently stands against anticipated requirements. Engage cybersecurity experts to perform a thorough gap analysis, comparing your current security posture, policies, and controls against the expected 2026 standards (e.g., NIST CSF, CMMC 2.0). This will identify weaknesses and prioritize areas for improvement.
2. Develop a Phased Compliance Roadmap
Based on the gap analysis, create a detailed, phased roadmap. Break down the compliance journey into manageable projects, assigning clear responsibilities, timelines, and budgets. Prioritize quick wins and high-risk areas first. A phased approach allows for continuous improvement and avoids overwhelming resources.
3. Invest in Technology and Automation
Leverage modern cybersecurity technologies to automate security tasks, enhance threat detection, and streamline compliance reporting. This includes:
- Advanced Threat Protection: Implement next-generation firewalls, EDR, and security orchestration, automation, and response (SOAR) platforms.
- Cloud Security Posture Management (CSPM): Ensure secure configurations and continuous monitoring of cloud environments.
- Vulnerability Management: Regularly scan for vulnerabilities and patch systems promptly.
- Data Governance Tools: Solutions for data classification, discovery, and access control to protect sensitive information.
4. Strengthen Your Human Firewall
Employees are often the weakest link in the security chain. Invest in continuous cybersecurity awareness training for all staff, from entry-level to C-suite. Topics should include phishing awareness, strong password practices, data handling protocols, and incident reporting procedures. Foster a culture where cybersecurity is everyone’s responsibility.
5. Implement a Robust Vendor Risk Management Program
Your supply chain is your extended attack surface. Establish a rigorous vendor risk management program that includes:
- Due Diligence: Thoroughly vet all third-party vendors for their cybersecurity practices before engaging them.
- Contractual Agreements: Ensure all contracts include strong cybersecurity clauses, audit rights, and incident notification requirements.
- Continuous Monitoring: Regularly assess and monitor vendor security posture throughout the contract lifecycle.
6. Embrace Zero-Trust Architecture
Federal agencies are increasingly advocating for zero-trust. This security model assumes that no user or device, whether inside or outside the network perimeter, should be trusted by default. Implement principles such as:
- Verify Explicitly: Authenticate and authorize every access request based on all available data points.
- Least Privilege Access: Grant users only the access they need to perform their job functions.
- Assume Breach: Design security with the assumption that breaches will occur and plan for rapid detection and response.
7. Prioritize Incident Response and Business Continuity
Even with the best preventative measures, incidents can occur. Develop and regularly test comprehensive incident response and business continuity plans. This includes:
- Clear Roles and Responsibilities: Define who does what during a cyber incident.
- Communication Plans: Establish protocols for communicating with stakeholders, regulators, and the public.
- Data Backup and Recovery: Implement robust backup strategies and test recovery procedures regularly.
- Tabletop Exercises: Conduct simulated cyberattack drills to refine response capabilities.
8. Engage with Legal and Compliance Experts
The legal and regulatory landscape is complex and constantly changing. Work closely with legal counsel specializing in cybersecurity law and compliance. They can help interpret regulations, ensure policies are legally sound, and advise on reporting obligations.
9. Allocate Sufficient Budget and Resources
Cybersecurity compliance is not a cost center; it’s an investment in business resilience. Secure adequate budget and resources for technology, personnel, training, and external services. Leadership buy-in and support are critical for successful implementation.
10. Stay Informed and Adapt
The threat landscape and regulatory environment are dynamic. Continuously monitor updates from federal agencies (e.g., CISA, NIST, OMB) and industry bodies. Be prepared to adapt your security posture and compliance strategies as new information and threats emerge.
The Strategic Advantage of Proactive Compliance
While the prospect of new Federal Cybersecurity Compliance 2026 standards might seem like another regulatory hurdle, it also presents a significant opportunity for forward-thinking US businesses. Those who proactively embrace these changes can gain a strategic advantage over competitors who lag. A robust cybersecurity posture built on compliance can:
- Enhance Customer Trust: In an era of data breaches, customers are increasingly prioritizing businesses that demonstrate a strong commitment to protecting their information. Compliance becomes a trust signal.
- Improve Business Resilience: Strong security controls and incident response capabilities reduce the likelihood and impact of cyberattacks, ensuring business continuity.
- Open New Business Opportunities: Meeting federal standards can qualify businesses for lucrative government contracts and partnerships that require high levels of security assurance.
- Reduce Insurance Costs: Demonstrating a mature cybersecurity program can lead to more favorable terms and lower premiums for cyber insurance.
- Foster Operational Efficiency: A well-defined security framework often leads to streamlined IT processes, better data governance, and improved overall operational efficiency.
- Attract and Retain Talent: A secure and compliant work environment can be a draw for top talent, especially in tech-savvy industries, as employees feel confident their data and work are protected.
By shifting the mindset from viewing compliance as a burden to seeing it as an investment in future growth and stability, US businesses can transform regulatory requirements into a powerful differentiator. The goal isn’t just to check boxes, but to embed security deeply into the organizational DNA, making it an integral part of operations and strategy.
Conclusion
The year 2026 will mark a pivotal moment for cybersecurity in the United States. New federal compliance standards are on the horizon, promising to significantly elevate the baseline for data protection and cyber resilience across various industries. For US businesses, this means a period of necessary adaptation, involving substantial investments in technology, personnel, and process improvements. The costs of compliance will be real, but the costs of non-compliance – ranging from crippling fines and reputational damage to loss of business and legal liabilities – are far greater.
Proactive preparation is key. By conducting thorough gap analyses, developing phased roadmaps, investing in advanced security technologies, strengthening human defenses through training, and building robust vendor risk management programs, businesses can navigate this changing landscape successfully. Embracing a zero-trust mindset and prioritizing incident response will be crucial elements of any effective strategy.
Ultimately, the Federal Cybersecurity Compliance 2026 standards are not merely about regulatory adherence; they are about building a more secure and resilient digital economy. For businesses willing to make the necessary investments and commit to continuous improvement, these new standards offer an unparalleled opportunity to enhance trust, mitigate risk, and secure a competitive edge in an increasingly interconnected and threat-laden world. The time to act is now, laying the groundwork for a secure and prosperous future.





